@bimipeg said in Question About Saving Fingerprint:
Hello everyone.
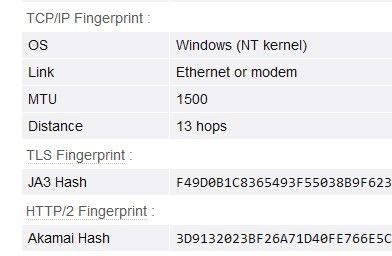
For one of my automation projects, I am saving fingerprint (using the key to grab the fingerprints in BAS) and cookie.
How can I use this same fingerprint and cookie again in fingerprint manager?
So basically : using bas I’m saving cookie and fprint and I want to usr these same cookie and fprint in manager software.
Only profiles can be used in FM, cookies, fingerprints and proxies are stored in them automatically. There is no functionality for downloading cookies separately, in FM.