I figured it out nvm. I just set this "\w{32}" as the regex but I actually clicked on the w/ button and then typed in the 32. Seems to work fine
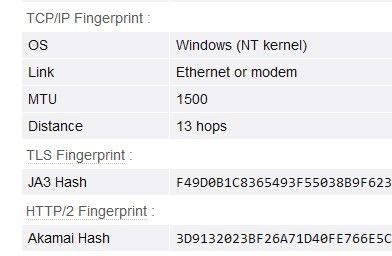
TLS/JA3, Akamai Hash and TCP/IP fingerprint
-
I have done some research in the forum, but I'm still not entirely clear on the current best practices for dealing with TLS fingerprints/JA3 hashes in BAS. I primarily use browser based bots with, only occasionally on pure HTTP requests. Is it indeed possible to identify BAS using TLS fingerprinting?
On browserleaks.com/ip, there is also an "Akamai Hash" (HTTP/2 Fingerprint) displayed. What significance does this have in automation, or can it be completely disregarded?
The so-called "TCP-IP Fingerprint" shouldn't be an issue, as it only shows OS, MTU, and less relevant values. Even though I work on a Windows machine, in most cases, I connect to the internet via a modem/router with a Linux-based OS (so OS = "Linux" should be fine even with a Windows OS). MTU 1500 is also a standard value.
-
@morpheus93 good question, let me know if you learn it